In October 1995, I finally found my calling. What I found was SQL Injection, perhaps the most prevalent web site hack still alive and well twenty years later. However, what I discovered was that my calling is not about hacking websites, but rather hacking humans.
Finding SQL Injection
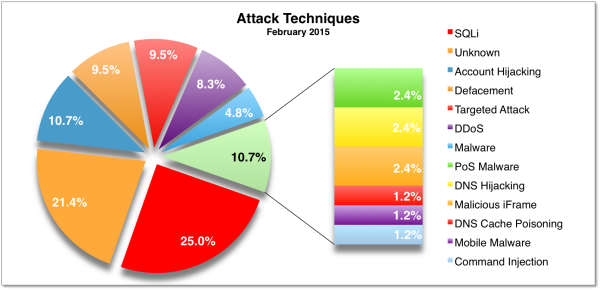
According to recent data, 25% of attacks still successfully use some variation of SQL Injection. My “discovery” of SQL Injection was like many discoveries, accidental. However, the reaction to my discovery, as with many security issues, was quite deliberate. To understand this, let’s jump into the DeLorean with Doc Brown and set the time machine to October, 1995.
In early 1995, I landed a job at Microsoft as technical writer working on this new “Internet” thing as part of the Microsoft Network (MSN). My job was to document the databases of some early e-commerce web properties, The Plaza at MSN and Microsoft Sidewalk. These were two of the first, large scale e-commerce sites available. This is a full year before Jeff Bezos founded Amazon.
My job was dull. I sifted through tables in the database (Microsoft SQL Server 6.0) validating data types. I documented the database structure, stored procedures, and other components in big reference manuals for the developers.
Being a technical writer is like being an outcast among outcasts. It is a difficult job that receives minimal respect among software developers. I committed to change that. I wanted to be a technical, technical writer—a writer who did not just fondle fonts all day, but dug into the code and learned the details, so I could communicate more effectively.
One afternoon, I was executing SQL queries on a development database. I used Notepad in Windows 95 (just released in August!) to write the queries and then copy/pasted into the query window. Most of my queries were fairly simplistic: SELECT * FROM product_sku; and so forth.
At some point, I tabbed over to Internet Explorer and pasted my query into a form field on the production website. I hit enter. The query was executed and the browser displayed the data. “Oh, that’s cool!” was my initial reaction. At that time the developers had built custom CGI handlers (in python and perl) to query data right from the HTML requests. For the next few days, I used this technique to do my work. It was much easier to use the browser directly.
Eventually, I pondered the inevitable question: “Would this work on other web sites?” With my dial up MSN account, I managed to hack about two dozen sites. Some of which were well-known tech companies. In the midst of my hackathon, I ran a query that displayed all the credit card numbers in a production website. Now, the gravity of this discovery has sunk in. This was not just a trick, it could be used for theft.
I demonstrated the hack to my manager, who was the Director of Operations for the site. He suggested I show it to the site developers. I sent around some emails and was invited to demonstrate SQL Injection at the next developer’s stand-up meeting.
On Tuesday October 10th, 1995 I stood in front of a team of developers at Microsoft and demonstrated a SQL Injection attack. The developer’s reaction to my demonstration, is why SQL injection still exists 20 years later:
“This is a waste of time,” barked one of the lead developers, “This is nothing. Go back to writing documents.”
“Yeah, who said you could do this stuff?” another developer yapped.
“We have the consultants from Accenture doing this stuff, this is not your job.”
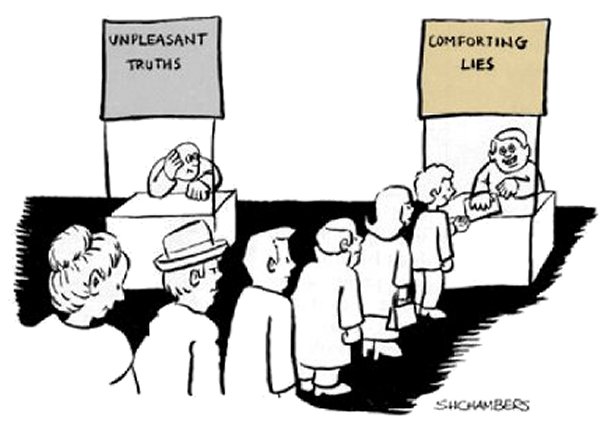
I was crushed. However, it is 20 years later and I am still having this meeting with disturbing regularity. I am still at the end of a conference room table describing reality, when all people want to hear is lies.
Comforting Lies
Information security often fails because people do not want to confront reality. They would rather hide inside false promises or security theater.
Recently, Anitian reviewed the previous security audits for a large company. The previous audit firm is well known, widely respected, and with big name investors. The audit was a complete fraud. The security controls in place are practically non-existent. For obvious legal reasons I cannot share any real names here. Suffice to day, this is not the first (or thousandth) time we have encountered this. Bad security is not merely common, it’s pervasive.
Like the developers I faced in 1995, many business leaders do not want information security reality. They certainly do not want some smartass (like me) showing them the problems. Because that means work. That means responsibility. That means liability. It is much easier to dismiss the smartass at the end of the conference room table, and find somebody who will tell you exactly what you want to hear.
The result? We have information security that is misinformation, immersed in illusions, and wrapped up in formality and compliance. The only way we ever confront truth is when the crime is complete, the breach is on Kreb’s Blog, and billions are lost. In all fairness, this has been the challenge of security for millennia. People do not acknowledge the threat until the ground is wet with the blood of its victims.
Security has devolved to the point where only ludicrous stunt hackers get any attention. Consider the recent and depressing case of Chris Roberts. Chris is a respected, intelligent security expert who was genuinely concerned about the security of airplanes. The only way his message could be heard was when he did something illegal. On one hand, Chris’ actions were wrong (and Anitian was critical of those actions). However, his actions were also symptomatic of why information security still struggles with a 20-year-old vulnerability. It is too easy to dismiss the truth through excuses and “messaging.” I am sure the airplane companies hired big important somebodies to validate, secure, and certify their networks. And I am sure when somebody raised the issue of gaining access to flight systems, there was a developer in that room yelling “this is a waste of time, go back to proactively leveraging your best-of-breed synergies, or whatever it is you do.”
Of course, we have mountains of security technologies now. In 1995 there were no web application firewalls, next-generation firewalls, or kill-chain endpoint security advanced protection malware defense platforms. In 2015, we have a Moscone Center filled to the roof with innovative technologies, that still cannot stop a SQL injection attack and a breach at one of the largest retailers (healthcare, government agencies, financial institutions, take your pick) in the world. Although we all implicitly know that technology is only as good as the user, it does not matter. VARs keep pushing products, people keep buying them, and the cycle of illusions just accelerates.
Likewise, conducting round after round of compliance assessments, penetration tests, and risk assessments does absolutely nothing for improving security if the people conducting those tests want to control the whole process and dismiss away the real problems. Exacerbating this is a whole, extremely profitable, industry of checkbox auditors who, for a price, will do or say whatever you want.
A Struggle for Truth
There is a great quote from Gandhi (thank you Kat Burgess for introducing me to this quote): “Be the change you want to see in the world.” For security people, it means you must embody the behaviors and attitudes you desire in other people. If you want to be respected, then respect others. If you want to be heard, then listen. If you want to be followed, then lead.
Mostly, if you want people to take data security seriously, then be serious about security. That means pushing yourself, your team, and your company to get better. It means putting the needs of the many (your employer) ahead of the needs of the few (you). It also means seeing every weakness as an opportunity to improve, not a fundamental character flaw.
In retrospect, my SQL Injection discovery seems like ancient history. However, the lessons from it have remained disturbingly constant. Ours is not a struggle of performance, technology, or compliance; ours is a struggle for truth. We must reject the illusions and seek truth – objectively verifiable truth.
This is why we have devoted ourselves at Anitian to building great security leaders and embracing scientific methods of analysis. The future of information security is not another technology innovation—it is a human innovation.
We must build leaders who:
- Place reason ahead of personal ambition
- Give everybody a seat at the table
- Confront hard truths
- Build trust and inspire others to greatness
- Are fearless in the face of pressure to cut corners and jeopardize security
Join our mission and be the change you want to see in the world.
October 2015 marks Anitian’s 20th Anniversary. As the oldest information security firm in the nation, we have seen enough to remain skeptical of our advancements, yet hopeful that reason and intellect will triumph in the long run.



4 thoughts on “Illusions of Information Security – The Struggle for Truth”
Great post about some of the human behavior challenges that co-mingles with the technical challenges of infosec. As Fleetwood Mac would say “Tell me lies, tell me sweet little lies”
I enjoyed the story about the SQLi, you have street creds.
Today, as always, unless it effects everyone as an individual, they could not be bothered. I am an independent security consultant who advises my clients on how to ‘seal up’ vulnerabilities and they value my opinion, but only because they have been ‘bit’ in the past with grave consequences. This is the same in real life as it is with online. People don’t want to worry about things they cannot see and they are surprised by the life changing events of stolen identity, corporate intellectual property or even tax refund theft.
There will always be a fight to teach people what is wrong, and that is what will keep us in business. The ego of the corporate identity and the individual. This can NOT be changed, but your marketing and approach to explain your value to the market CAN change and CAN truly speak to these people if you write it the correct way.
By the way – this is an excellent quote you put in your article:
““We have the consultants from Accenture doing this stuff, this is not your job.””
This is why they only had 8 people working on OS security in 2002, and this is why they continue to be plagued with security breaches, they don’t care about security like a security expert can. They do more today than ever before, but it is not a priority. Case in point – look at what Windows 10 tried to link to in the background!
Very interesting story .. but most ‘ end users ‘ are not so bothered about security or web security as they are just users and Internet Security is usually handled by IT departments in corporate world. Often times people in higher positions ‘do not want to hear truths’ until a serious breach occurs. Good post.
So here is an idea. Database servers take the incoming SQL query and run it through a parser resulting in a parse tree. Then they turn the tree into a plan and execute the plan.
The essence of injection is that the parser produces a tree different from the one intended by the programmer.
So the fix is to be able to detect unusual parse trees. Walk the tree after parsing and produce a string in canonical form minus the data values. Compute a SHA hash of the string. Keep a table of known hashes for the application/database user. Warn or abort if the server sees an unknown hash.
Obviously, there is a startup problem. So the programmer would have to run the application in a testing mode, extract the hashes after exhaustive testing, and the load the server with the hashes on application startup. Then turn on abort-on-new-hash and no more SQL inject should be possible.