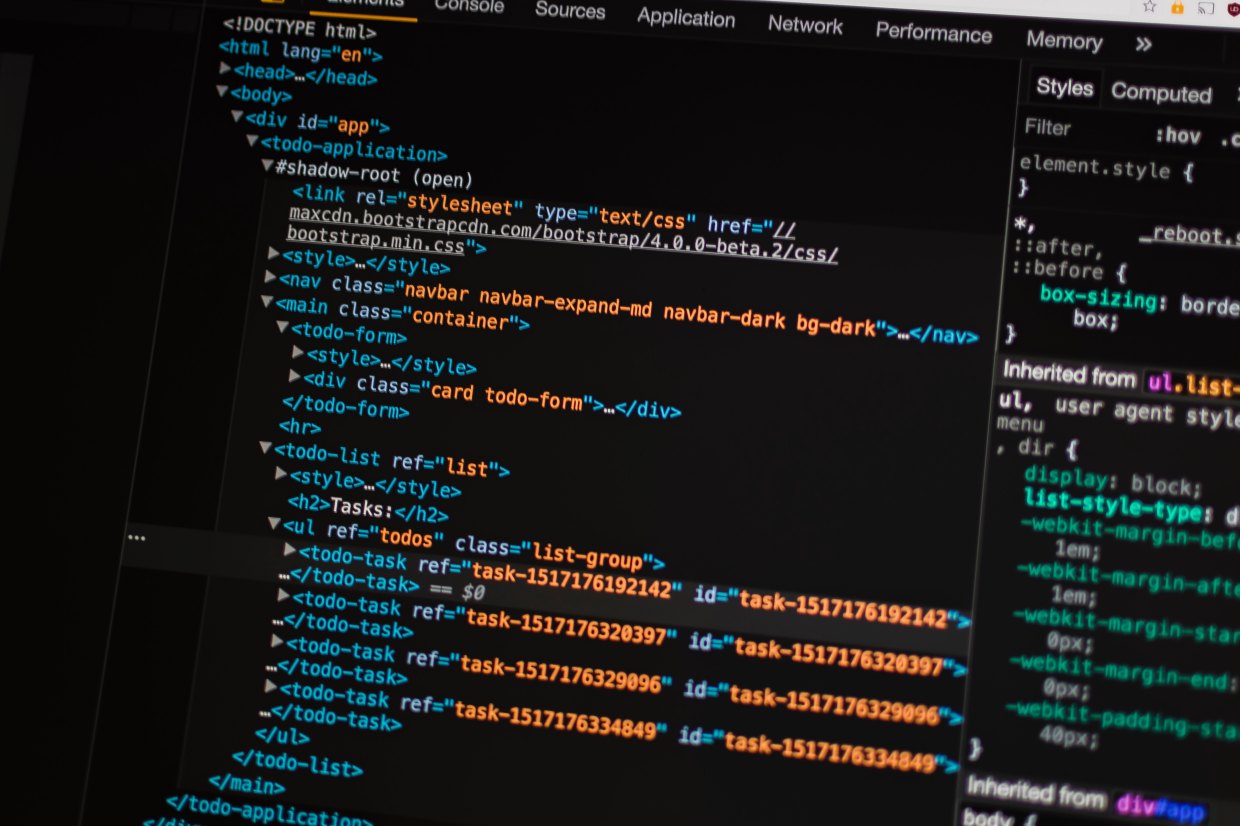
We return to hacking SQL servers, with a whole new script that automates the attack.
Future SOC
People passively monitoring alerts is not an effective SOC strategy. We need a Future SOC.
Nuke the Checkbox Audit from Orbit, or Alienate the Millennials
Millennials have a high affinity for authentic leadership. That means your information security program must also be authentic. Purging the practice of checkbox audits is one change that will keep your Millennial workforce engaged.
Hacking Nagios: The Importance of System Hardening
A recent penetration test uncovered some serious vulnerabilities in a Nagios deployment and served as a reminder that system hardening is vital to good security.
Hacking Microsoft SQL Server Without a Password
Using a Man in the Middle (MITM) style attack and some packet manipulation, you can hack any Microsoft SQL Server and setup shop.
Digging Deeper – Striking Gold in Penetration Testing
Sometimes automated scanners cannot detect subtle vulnerabilities embedded deep inside scripts. It pays to dig a little deeper to strike vulnerability gold.
Illusions of Information Security – The Struggle for Truth
In October 1995, I finally found my calling. What I found was SQL Injection, perhaps the most prevalent web site hack still alive and well twenty years later. However, what I discovered was that my calling is not about hacking websites, but rather hacking humans.
Anatomy of a Hack: Cross-Site Request Forgery (CSRF)
Cross-Site Request Forgery is a common vulnerability that many web application scanners can miss. In this real-world example, Anitian demonstrates how multiple CSRF attacks can be chained together to create a more serious attack.
Enough with the Stunt Hacking
The time has come for the information security profession to reject stunt hacking such as the sensational car hacks that Charlie Miller and Chris Valasek performed.
PCI Compliance for the AWS Cloud
Anitian’s Workbook for PCI Compliance in the AWS Cloud takes the guesswork out of making your AWS infrastructure PCI DSS compliant.