In just a few hours, Anitian customers can use Anitian Compliance Automation to build out an entire cloud environment that is pre-configured to meet a rigorous set of compliance and security requirements, as defined in the PCI DSS. Link to release via PRWeb PORTLAND, OR — November 20, 2018 — Anitian, an Oregon-based security intelligence […]
Anitian Completes FedRAMP Deployment for SaaS Company, Smartsheet, Using New Compliance Automation Platform in AWS GovCloud in Under 60 Days
Anitian, an Amazon Web Services Partner Network Advanced Consulting Partner, completed a FedRAMP deployment for SaaS company, Smartsheet, using Anitian’s new Anitian Compliance Automation platform in AWS GovCloud (US) Region in under 60 days. Link to release via PRWeb PORTLAND, OR — NOVEMBER 27, 2018 — Anitian, a security intelligence and automation firm, announced today […]
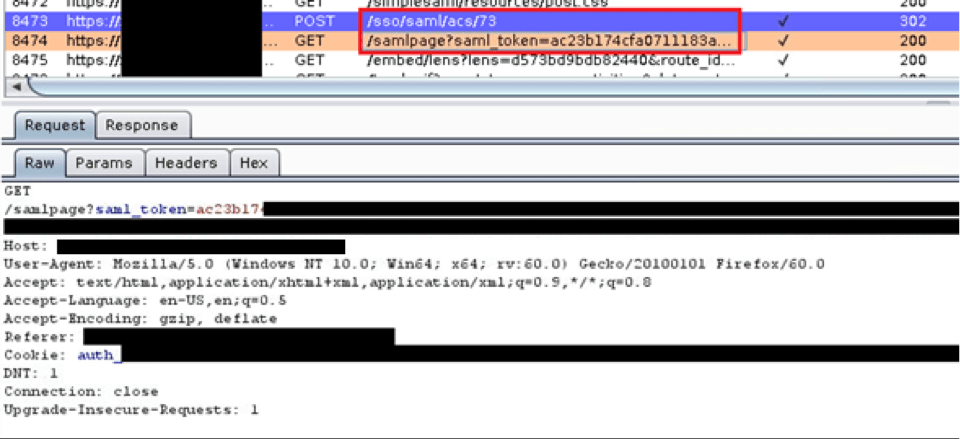
Owning SAML
Exploiting a SAML Implementation and SAML Vulnerability During a recent web application test, I discovered a bug in a Security Assertion Markup Language (SAML) implementation. This bug involved an insecure implementation of a SAML feature combined with a custom authentication mechanism our client developed out of a need to support their customers. With a bit […]
The NGFW is Dead
Let’s get this out of the way: the next-generation firewall (NGFW) is dead. The cause of death: cloud. However, this is not an execution, rather a slow, decline into irrelevance in the face of a more agile competitor. The shroud of death and decay are all around the NGFW products. They are bloated, expensive, and […]
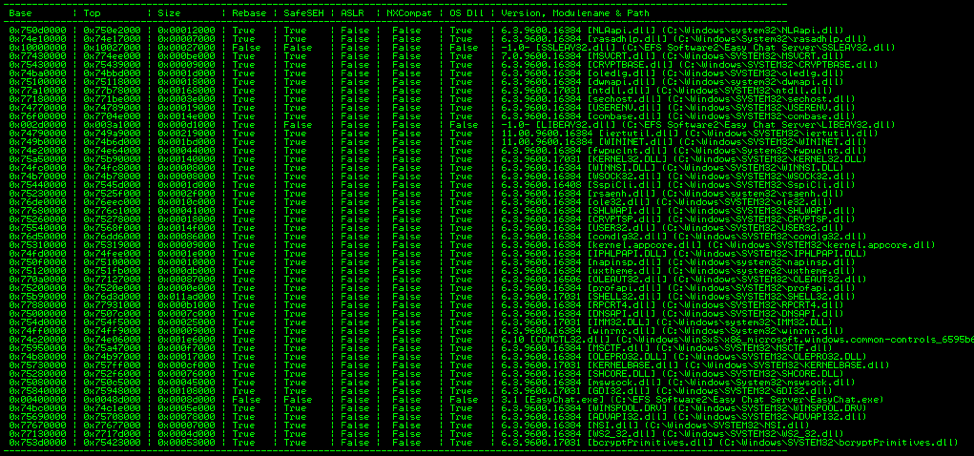
A Study in Exploit Development – Part 2: Taking it to the Next Level
Welcome to Part 2 of this 2-part blog series looking at the details of exploring and validating an exploit! If you liked this series, I bet you’d be interested in our webinar on How to Think Like A Hacker, check it out! Now on to Part 2: Taking it to the Next Level. (Part 1 […]
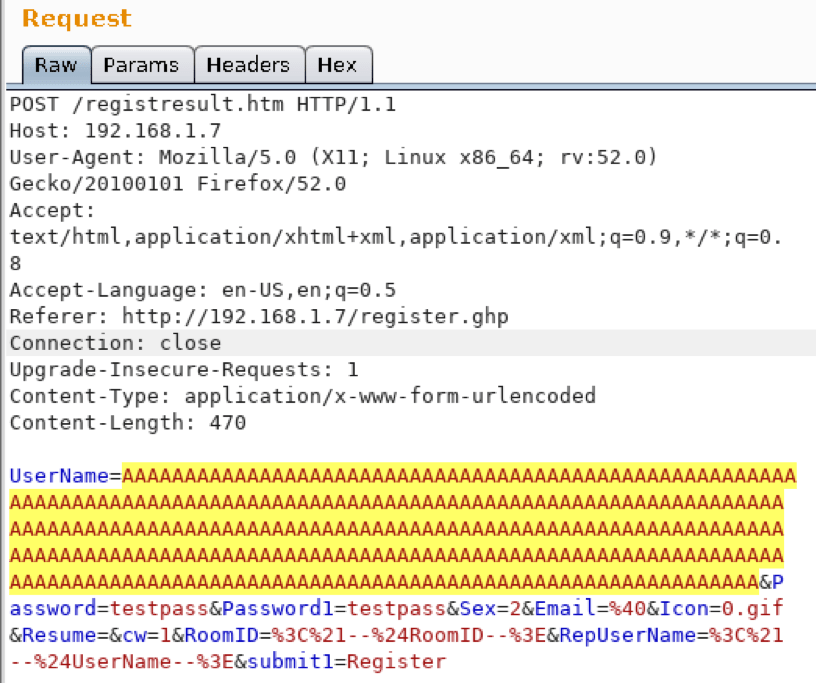
A Study in Exploit Development – Part 1: Setup and Proof of Concept
A Study in Exploit Development: Easychat SEH exploit A typical penetration test involves automated compliance scanning to identify vulnerabilities, followed by a more manual testing process where the tester attempts to validate and exploit those vulnerabilities. Many times, we discover vulnerabilities with publicly available exploits. This can sometimes result in a complete domain compromise. Other […]
The Top Five SOC 2 Compliance Questions Answered
SOC2 compliance is a must-have for SaaS companies. Anitian’s VisionPath compliance team looks at your road to SOC2 compliance.
How to Make PCI Compliance a Little Easier for Everyone
Before we begin, there’s one thing to make very, very clear: You cannot outsource ALL compliance! I do not care what some vendor says. No single service makes you compliant. Only you can make you compliant. While vendors can take you most, if not all the way to compliance. You must still confirm their compliance […]
The Human Firewall is a Lie
It is delusional to think we can deprogram millennia of human evolution because information security is difficult. The human firewall is a lie.
Ulterius Zero Day Disclosure
How Anitian discovered a zero day vulnerability in the Ulterius remote access software, and wrote an automated exploit tool.